
As businesses are moving business processes and storing date on the Cloud. Having a good email service provider is essential. For our customers using Google and future customers that wish to engage us to manage their Google Workspace, we will recommend Google Enterprise for the best Security management and compliance controls that Google has to offer.
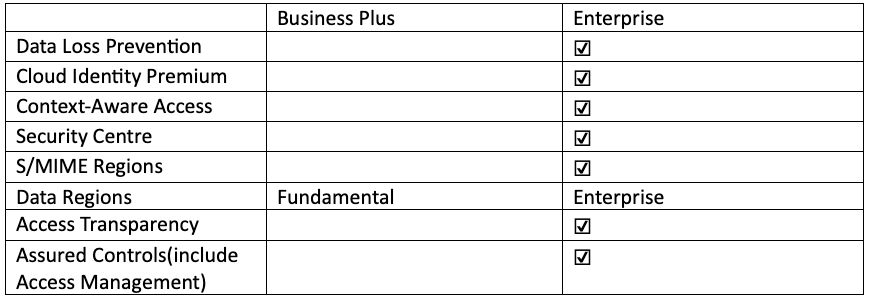
Below is a table for the breakdown of features that are present in the enterprise version:
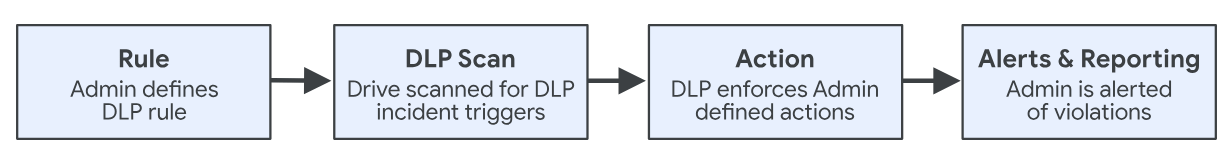
Using Google Workspace’s Data Loss Prevention,
- Able to define and apply rules to control content that users share in files outside of the organization.
- Gives admin control on what users can share and prevents unintended leak of sensitive information
- Rules will trigger scanning of files for sensitive information and prevent users from sharing that content
- Rules will also determine the nature of incidents and its trigger action:
- Blocking of content
- Quarantine of content
- Receiving alerts for DLP rule violations
Google Cloud Identity
- Manage users, apps and company devices from Google Admin Console
- Premium features include:
- Allow recommended apps and make them available for installation
- Manage company owned devices
- View mobile log event data
- Define rules to automate mobile management
- Browse software as a service apps (SaaS)
- Set session length
Context-Aware Access for Users
Google Workspace admins are able to control which apps specific user can access based on context, such as whether individual devices comply with IT policy.
Creates granular access control policies for apps that access Workspace data includes:
- User identity
- Location
- Specific countries where a user can access the apps
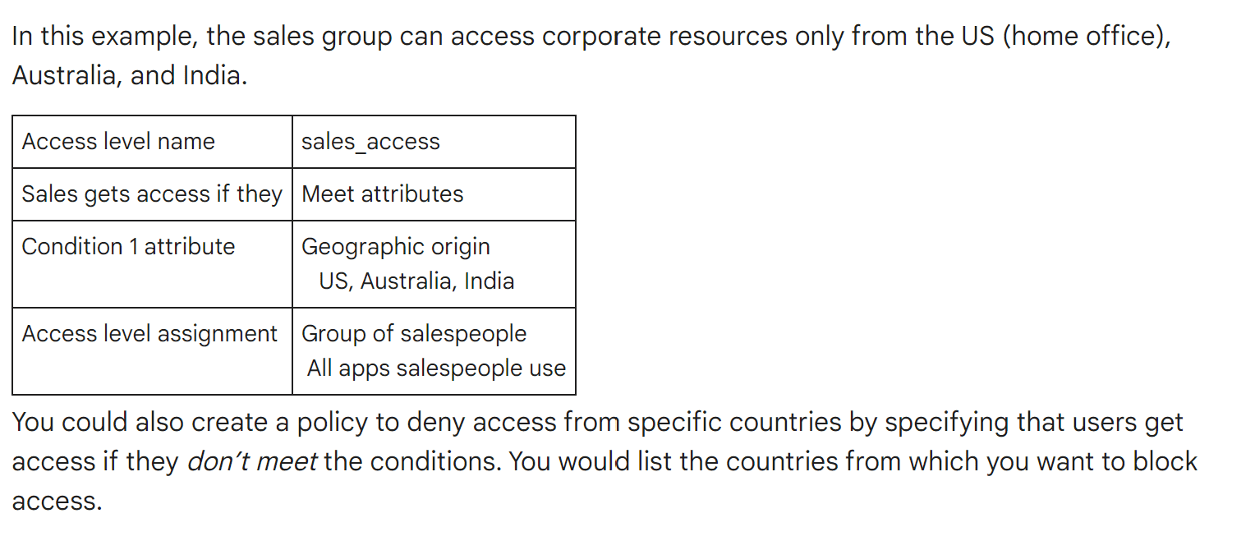
- BYOD policy and Device OS – specify parameters required for a device to be able to access an app:
- Requirement of password
- Requirement of having the latest Apple iOS or Android operating system
- Requirement of device encryption
- IP address – specifies an IP address range from which a user can connect to an app
Google Security Center
Dedicated security dashboard, investigation tool and security health:
- Expands on advanced settings in Admin Console to view security data through customizable reports
- Monitor configurations of Google Admin console settings from Security Health Page
- Uses investigation tool to identify and take action on security/privacy issues found in logs and search results
S/MIME message encryption with Google Workspace
Additional layer of protection from email threats:
- Encrypting and adding digital signature to messages
- Messages decrypted using combination of public and private keys
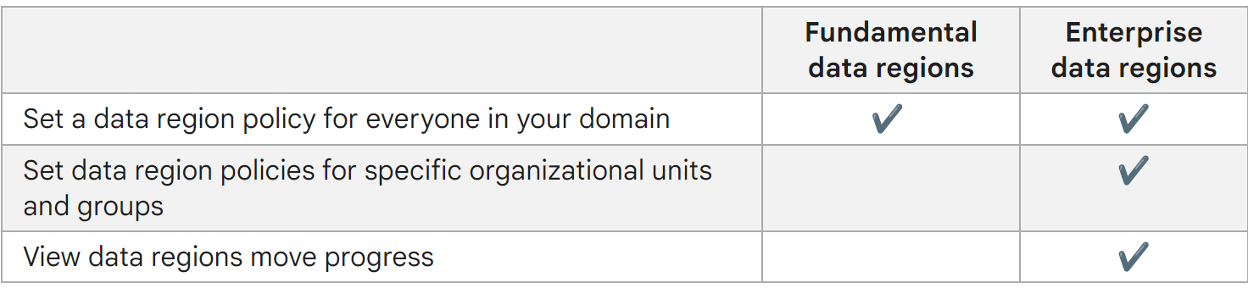
Data Regions for Google
- Able to store covered data in specific geographic location by using data region policy
- United States or Europe as options
Before implementing data region policy, Google Workspace admins should take note that:
- Users outside the region where their data is located and stored might experience higher latency
- Editing shared documents in real time
- Sharing files outside of data region
- Travelling internationally
Access Transparency by Google
Review logs of actions taken by Google staff when accessing user content:
- Actions by Support Team that user requested
- Engineering investigations into your support requests
- Other investigations made for valid business purposes
Here at Entrust, we are more than capable of configuring and customising Google Workspace to your needs. Email security is crucial in today’s rapid digitalisation. Do contact us about Google Workspace and we will present you a comprehensive security solution that would satisfy your requirements for productivity and security.

